[ad_1]
It’s each researcher’s worst nightmare. A careless click on on an e-mail and years of laboratory information are instantaneously encrypted by hackers. Or a bit of legacy lab tools is compromised by its historic, zero-security connection to the Web. The machine might need been a godsend for working experiments from dwelling throughout the COVID-19 pandemic, however now it’s an open door to those that want to exploit your institutional intranet. On this viral an infection, you, embarrassingly, are affected person zero.
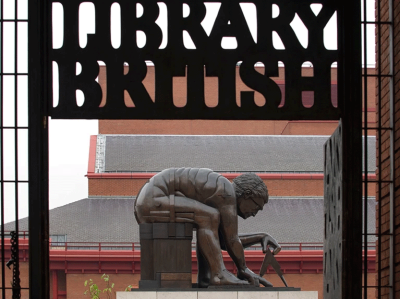
The record of hacked educational establishments, analysis centres and infrastructure makes alarming studying. It consists of the Faculty of Drugs on the College of California, San Francisco (UCSF); the Fred Hutchinson Most cancers Middle in Seattle, Washington; the Berlin Museum of Pure Historical past; the Atacama Massive Millimeter/submillimeter Array (ALMA) telescope in Chile; the Japan Aerospace Exploration Company in Tokyo; the College of Wollongong in Australia; and the British Library in London.
Cyberattacks on information establishments are rising: what could be finished?
However that record hardly scratches the floor — and definitely doesn’t replicate the various incursions which were tried. Analysis establishments are primarily underneath siege. “On the College of São Paulo, there are each day makes an attempt to breach safety protocols,” says Ildeberto Aparecido Rodello, director of the Info Know-how Middle on the college’s Ribeirão Preto campus in Brazil. The identical goes for CERN, Europe’s particle-physics lab close to Geneva, Switzerland. “We’ve been fortunate up to now couple of years that we haven’t had any breaches that are price calling a breach,” says Stefan Lueders, CERN’s head of laptop safety. “There are attackers outdoors who’re always probing the group for weaknesses.”
It may be exhausting to understand the dimensions of those operations, says James Fleming, chief info officer on the Francis Crick Institute in London. “The sort of actors who carry out cyberattacks at scale are massively environment friendly: they automate the overwhelming majority of their processes,” he says. “The information our firewall collects exhibits that bots try completely different passwords to log onto accounts and completely different programs, or looking for the vulnerabilities, tens of 1000’s of instances every week.”
The issue is, universities and different analysis establishments could be tender targets. They thrive on data-sharing and openness and have an enormous and extremely cell workforce, most of whom are much less centered on cybersecurity than on the power to entry their programs from wherever they occur to be. “We’re right here to share analysis and we’re open by design, which makes us weak to cybercrime,” says Sarah Lawson, chief info safety officer at College School London. “Training has been closely focused over the previous couple of years, and the statistics inform us that that’s on the rise.”
What’s extra, she provides, universities haven’t conventionally invested in cyber defence, placing them on the again foot in what she likens to “a recreation of whack-a-mole”: finally, you will lose. “It’s not if,” she says, “it’s when.”
Devastating penalties
When that occurs, the results could be catastrophic. In a ransomware assault, for example, valuable information may very well be stolen or encrypted in order that they can’t be accessed, except the file proprietor pays the attacker. “You actually have only a few choices,” Fleming says. “You possibly can both simply wipe every little thing and take the hit, or you may find yourself with a monetary penalty.” UCSF took the second possibility after a 2020 breach of their programs, selecting to pay a ransom of US$1.14 million.
But when every little thing is backed up and no delicate information have been compromised, the primary possibility won’t be too unhealthy, Fleming says. “You hard-wipe all of the machines and reformat all of the exhausting drives, and then you definitely do a rebuild. You perhaps lose every week of productive time.”
That does rely upon the dimensions of the assault and the preparedness of your establishment, nevertheless. The British Library is now performing a “full technical rebuild and restoration” on its digital infrastructure after an October 2023 cyberattack, which occurred because the library was updating its core expertise infrastructure. “The work will now be accelerated,” a spokesperson advised Nature. It’s too early to say how lengthy that can take or what it would price, they add, however The Monetary Occasions has estimated a price ticket of round £7 million (US$9 million).

The British Library in London has needed to rebuild its digital infrastructure after a cyberattack in October 2023.Credit score: Previous City Vacationer/Alamy
Recovering from the assault on the ALMA observatory, which occurred in October 2022, took “a bit lower than seven weeks”, in line with Jorge Ibsen, head of ALMA’s computing division. However the monetary hit can solely be guessed at, he says. “The most effective estimate can be 13% of the annual operational price, which is the fraction of days inside a yr we couldn’t ship to our mission.” As for particulars of what the restoration entailed, and the measures taken since, Ibsen is eager to maintain them underneath wraps. “Given the character of this menace, we can’t additional talk about particulars about our particular cybersecurity technique,” he says.
Institutional cyberattacks don’t all the time finish with a ransom cost or rebuild of digital infrastructure. For one factor, paying a ransom doesn’t essentially preclude unhealthy actors from weaponizing or releasing information. And there may very well be authorized repercussions. For example, some individuals who had been affected by the assault on the Fred Hutchinson Most cancers Middle, in November 2023, have filed class-action lawsuits towards the centre.
Unplug and shut down
What concerning the people who’re compromised? When it occurs to you, what do you have to do? Unanimously, these heads of cybersecurity plead that you just talk with them — after turning off and disconnecting no matter system has been hacked. “Pull out the plugs and shut it down. Shut it after which search recommendation,” Lawson says.

11 methods to avert a data-storage catastrophe
That mentioned, prevention is all the time higher than remedy, and a correctly ready human generally is a highly effective firewall. “Replace your software program usually; implement firewall and antivirus options; management entry and permissions to your programs; encrypt delicate information,” Rodello says. He even suggests participating cybersecurity specialists to conduct common audits and supply steerage on enhancing your lab’s digital security.
In spite of everything, most lecturers will not be skilled IT professionals, and DIY options could be harmful. Lawson says she will’t assist however admire cybercriminals’ skill to govern their targets. “They’re the perfect psychologists on this planet,” she says. “They’ll use each approach within the e-book to seek out the best way into your cash. And so they’re actually good at it.”
It may appear apparent, however one other tip is to again up information someplace safe — and, if attainable, someplace off-site. And don’t overlook the software program you wrote your self. “Ideally, folks use correct software program libraries they usually run exams to verify of its safety,” Lawson says. “However we do have issues with individuals who don’t take into consideration that.” Nice researchers, she appreciates, are not often centered on the truth that many criminals are out to smash their lives.
Evolving threats
These working within the health-care sector are at particularly excessive danger. “The health-care system at the moment is without doubt one of the number-one targets for hacking due to the monetary profit that individuals can acquire from getting a well being report,” says Anthony Cartwright, an anaesthesiologist on the Cleveland Clinic in Abu Dhabi, United Arab Emirates, who has written concerning the cybersecurity dangers in well being care (A. J. Cartwright J. Clin. Monit. Comput. 37, 1123–1132; 2023).
Some vulnerabilities arose throughout the COVID-19 pandemic, Cartwright says, when many hospital workers started working from dwelling. In lots of circumstances, these programs haven’t been up to date. “They’re now accessing hospital community programs on an unsecured private community. Usually, that laptop in the home can be shared between the mum, dad, brother or sister.” In different phrases, something might get on there.
Such programs must be up to date, in fact. However don’t overlook common sense precautions, comparable to holding passwords non-public. Cartwright was struck by a tv section filmed in a hospital throughout the pandemic. “Because the digital camera panned round to one of many nurses on the management desk, there was a bit of paper giving the password — and you might learn it on display,” he says. “The Wi-Fi password was proper there, on TV.”
NatureTech hub
That mentioned, due to authorities initiatives such because the 1996 US Well being Insurance coverage Portability and Accountability Act (HIPAA), health-care employees are sometimes extra security-savvy than are educational researchers, reckons Anton Dahbura, government director of Johns Hopkins College’s Info Safety Institute in Baltimore, Maryland. “It’s way more prime of thoughts and it’s been instilled within the tradition.”
On the identical time, nevertheless, unhealthy actors are getting extra refined. Though some hacks are for sport or to advance a political agenda — hacktivists concentrating on scientists engaged on controversial analysis, for example — cybersecurity professionals are more and more involved about state-level actors whose purpose is to destabilize crucial infrastructure or steal mental property. “Universities maintain a variety of vital, proprietary and delicate info,” Dahbura says. Scientific analysis institutes comparable to genomics labs “maintain info that adversaries, specifically nation states, would like to have”, he factors out. “It’s no completely different than hacking right into a analysis and growth lab of a pharmaceutical firm, besides that it’s in all probability simpler at a college.”
Regardless of the motivation, nobody desires to be the one who let an attacker in. Lueder provides a easy mantra: “Cease, suppose, don’t click on!” That is the way you stop the vast majority of hacking makes an attempt, he says. “The Web has made us all so curious that we click on on issues with out realizing what they’re. The mind could be actually silly.”
[ad_2]
Supply hyperlink



