[ad_1]
Right this moment, I’m excited to announce the general public preview of our unified safety operations platform. Once we introduced a restricted preview in November 2023, it was one of many first safety operations heart platforms that introduced collectively the complete capabilities of an industry-leading cloud-native safety data and occasion administration (SIEM), complete prolonged detection and response (XDR), and generative AI constructed particularly for cybersecurity. This highly effective mixture of capabilities delivers a really unified analyst expertise within the safety operations heart (SOC).
And final month at Microsoft Safe, we added unified publicity administration capabilities that present steady, proactive end-to-end visibility of property and cyberattack paths. Collectively, these totally built-in, complete capabilities give safety leaders and SOC groups what they should handle cyberthreats throughout their group—from prevention to detection and response.
After gaining insights from the preliminary buyer suggestions, we’re excited to develop the platform’s availability to public preview. Prospects with a single Microsoft Sentinel workspace and at the very least one Defender XDR workload deployed can begin having fun with the advantages of a unified expertise, in a manufacturing setting, now. Onboarding a Microsoft Sentinel workspace solely takes a couple of minutes, and clients can proceed to make use of their Microsoft Sentinel in Azure. Want another excuse to get began at present? Microsoft Sentinel clients utilizing Microsoft Copilot for Safety can now leverage the embedded expertise within the Defender portal, serving to them to stage up their safety follow additional.
Unified safety operations platform
The brand new platform brings collectively the capabilities of XDR and SIEM. Learn to onboard your Microsoft Sentinel workspace to the Microsoft Defender portal.

Knock down safety silos and drive higher safety outcomes
SOCs are buried underneath mountains of alerts, safety alerts, and initiatives. Analysts are spending an excessive amount of time sifting by way of low-level alerts, leaping between portals, and navigating complicated workflows to know what occurred, resolve it, and stop it from taking place once more. This leaves little time for analysts to deal with high-value duties—like remediating multistage incidents totally and even reducing the chance of future assaults by decreasing the assault floor. With an ever-growing hole in provide and demand of expertise—in reality, there are solely sufficient cybersecurity professionals to fulfill 82% of the USA demand—one thing should change.1
On the coronary heart of this problem is siloed information—SOCs have an excessive amount of safety information saved in too many locations and most SOC groups lack the instruments to successfully convey all of it collectively, normalize it, apply superior analytics, enrich with risk intelligence, and act on the insights throughout your complete digital property. This is the reason we constructed the safety operations platform—by bringing collectively the complete capabilities of SIEM, XDR, publicity administration, generative AI, and risk intelligence collectively, safety groups might be empowered with unified, complete options that work throughout use instances, not safety device siloes.
The brand new analyst expertise is constructed to create a extra intuitive workflow for the SOC, with unified views of incidents, publicity, risk intelligence, property, and safety reporting. This can be a true single pane of glass for safety throughout your complete digital property. Past delivering a single expertise, unifying these options all on one platform delivers extra strong capabilities throughout your complete cyberattack lifecycle.
“Safety groups want a single pane of glass to handle at present’s IT environments. Lengthy gone are the times when groups might function in silos and shield their environments. With at present’s announcement Microsoft is shifting one other step ahead in serving to companies shield their methods, clients and reputations,” mentioned Chris Kissel, IDC Analysis Vice President, Safety and Belief. “Microsoft combining the complete capabilities of an industry-leading cloud-native SIEM and XDR with the primary generative AI constructed particularly for cybersecurity is a recreation changer for the {industry}.”
Capabilities throughout Microsoft Sentinel and Microsoft Defender XDR merchandise at the moment are extending, making each Microsoft Sentinel and Defender XDR extra precious. XDR clients can now get pleasure from extra flexibility of their reporting, their capacity to deploy automations, and higher perception throughout information sources. With the brand new capacity to run customized safety orchestration, automation, and response (SOAR) playbooks on an incident offered by Microsoft Sentinel, Defender XDR clients can scale back repetitive processes and additional optimize the SOC. They’ll additionally now hunt throughout their XDR and SIEM information in a single place. Additional, XDR detection and incident creation will now open to information from SIEM. SIEM clients can now get extra out of the field worth, enhancing their capacity to deal with the duties at hand and acquire extra proactive safety in opposition to threats, releasing them to spend extra time on novel threats and the distinctive wants of their setting.
Stop breaches with end-to-end visibility of your assault floor
In the course of the previous 10 years, the enterprise assault surfaces have expanded exponentially with the adoption of cloud companies, bring-your-own machine, more and more complicated provide chains, Web of Issues (IoT), and extra. Roughly 98% of assaults might be prevented with primary cybersecurity hygiene, highlighting the significance of hardening all methods.2 Safety silos make it tougher and time-consuming to uncover, prioritize, and remove exposures.
Luckily, the Microsoft Safety Publicity Administration answer, constructed proper into the brand new unified platform expertise, consolidates silos right into a contextual and risk-based view. Inside the unified platform, safety groups acquire complete visibility throughout a myriad of exposures, together with software program vulnerabilities, management misconfigurations, overprivileged entry, and evolving threats resulting in delicate information publicity. Organizations can leverage a single supply of reality with unified publicity insights to proactively handle their asset threat throughout your complete digital property. As well as, assault path modeling helps safety professionals of all ability ranges predict the potential steps adversaries could take to infiltrate your important property and attain your delicate information.
Shut down in-progress assaults with computerized assault disruption
In at present’s risk panorama, the place multistage assaults are the brand new regular, automation is not non-obligatory, however a necessity. We’ve seen complete ransomware campaigns that solely wanted two hours to finish, with attackers shifting laterally in as little as 5 minutes after preliminary compromise—the median time for attackers to entry delicate information is barely 72 minutes.3 This functionality is crucial to counter the fast, persistent assault strategies like an AKIRA ransomware assault. Even the perfect safety groups must take breaks and with mere seconds separating hundreds versus tens of millions of {dollars} spent on an assault, the velocity of response turns into important.
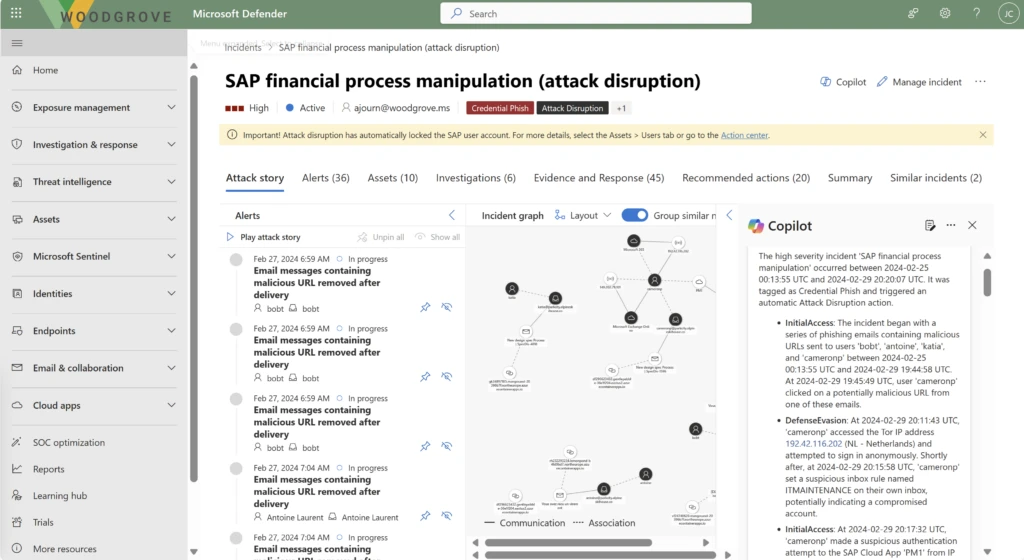
This platform harnesses the ability of XDR and AI to disrupt superior assaults like ransomware, enterprise e mail compromise, and adversary-in-the-middle assaults at machine velocity with computerized assault disruption, a game-changing expertise for the SOC that continues to be unique to Microsoft Safety. Assault disruption is a strong, out-of-the-box functionality that mechanically stops the development and limits the affect of essentially the most subtle assaults in close to real-time. By stopping the assault development, treasured time is given again to the SOC to triage and resolve the incident.
Assault disruption works by taking a large breadth of alerts throughout endpoints and IoT, hybrid identities, e mail and collaboration instruments, software program as a service (SaaS) apps, information, and cloud workloads and making use of AI-driven, researcher-backed analytics to detect and disrupt in-progress assaults with 99% confidence.3 With greater than 78 trillion alerts fueling our AI and machine studying fashions, we will quickly detect and disrupt distinguished assaults like ransomware in solely three minutes, saving hundreds of units from encryption and restoration prices. Utilizing our distinctive capacity to acknowledge the intention of the attacker, that means precisely predict their subsequent transfer, Microsoft Defender XDR takes an automatic response equivalent to disabling a consumer account or isolating a tool from connecting to every other useful resource within the community.
Constructed on the assault disruption expertise in our Defender XDR answer, our unified platform now extends this dynamic safety to new options by way of Microsoft Sentinel—beginning with SAP. When an SAP account assault is detected, our platform will mechanically reply to chop off entry in SAP. This implies unprecedented safety for a platform that homes extremely delicate information, making it a chief goal for attackers.
Examine and reply quicker
A number of dashboards and siloed looking experiences can actually decelerate the meantime to acknowledge and reply. The effectiveness of the SOC is measured by these important metrics. Microsoft delivers a single incident queue, outfitted with strong out-of-the-box guidelines, that saves time, reduces alert noise, and improves alert correlation, finally delivering a full view of an assault. Throughout our non-public preview, clients noticed as much as an 80% discount in incidents, with improved correlation of alerts to incidents throughout Microsoft Sentinel information sources, accelerating triage and response.4 Additional, unified looking helps clients to scale back investigation time by eliminating the necessity to know the place information is saved or to run a number of queries on completely different tables.
We’re not stopping at computerized assault disruption and unified incident queues—we’re on a mission to uplevel analysts of all expertise ranges. Microsoft Copilot for Safety helps safety analysts speed up their triage with complete incident summaries that map to the MITRE framework, reverse-engineer malware, translate complicated code to native language insights, and even full multistage assault remediation actions with a single click on.
Copilot for Safety is embedded within the analyst expertise, offering analysts with an intuitive, clever assistant than can information response and even create incident studies mechanically—saving analysts important time. Early adopters are seeing their analysts transfer a median of 22% quicker and speed up time to decision.5 Copilot for Safety is greater than a chatbot—it’s a real clever assistant constructed proper into their workflow, serving to them use their instruments higher, stage up their abilities, and get suggestions related to their work at hand.
In case you’d like to affix the general public preview, view the conditions and join your Microsoft Sentinel office.
Study extra
Study extra about Microsoft SIEM and XDR options.
To study extra about Microsoft Safety options, go to our web site. Bookmark the Safety weblog to maintain up with our professional protection on safety issues. Additionally, observe us on LinkedIn (Microsoft Safety) and X (@MSFTSecurity) for the most recent information and updates on cybersecurity.
1Cybersecurity Provide and Demand Warmth Map, CyberSeek. 2024.
2Microsoft Digital Protection Report, Microsoft. 2023.
3Microsoft Digital Protection Report, Microsoft. 2022.
4Microsoft Inside Analysis.
5Microsoft Copilot for Safety randomized managed trial (RCT) with skilled safety analysts performed by Microsoft Workplace of the Chief Economist, January 2024.
[ad_2]
Supply hyperlink

